In an increasingly digital age where government agencies and organizations handle sensitive information and critical operations online, ensuring the security and integrity of these systems is paramount. The Federal Risk and Authorization Management Program (FedRAMP) was established to address this need by standardizing security requirements for cloud services and products used by federal agencies. FedRAMP provides a framework that helps agencies assess the security of cloud offerings and authorizes their use based on different levels of risk. This article delves into the various FedRAMP authorization levels and helps organizations understand which one is the most suitable for their specific needs.
Table of Contents
Understanding FedRAMP Authorization Levels
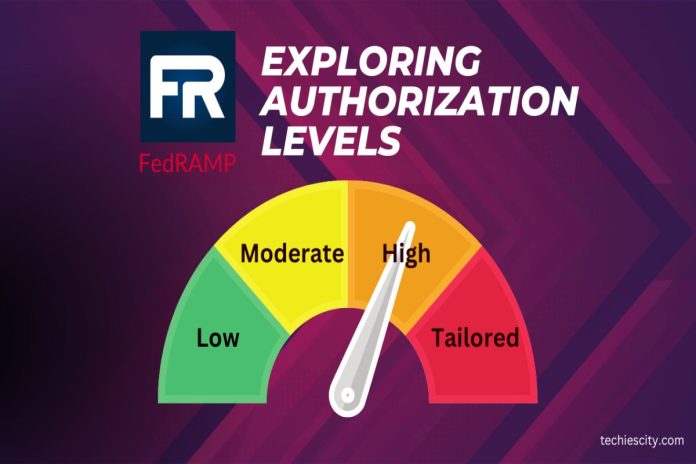
FedRAMP categorizes cloud services and products into different authorization levels based on the potential impact of a security breach. These authorization levels provide a structured approach to assessing and managing risk while also offering a flexible framework for cloud adoption. As of my last knowledge update in September 2021, there are four primary FedRAMP authorization levels, each tailored to address various risk profiles:
- Risk Level: Low
Description: FedRAMP Low is suitable for cloud services and products that handle non-sensitive, public information. This level is intended for systems that do not have a significant impact on an organization’s operations or individuals’ privacy. While security measures are in place, the potential consequences of a security breach are relatively minimal.
2. Risk Level: Moderate
Description: FedRAMP Moderate is designed for cloud services that handle sensitive but not classified information. This includes data that, if breached, could lead to financial loss, damage to an agency’s reputation, or violation of privacy laws. The security requirements at this level are more stringent than FedRAMP Low, reflecting the higher level of risk associated with the data being processed and stored.
3. Risk Level: High
Description: FedRAMP High is the level for cloud services that handle highly sensitive information, including classified data. This level is relevant for systems that, if compromised, could have a severe impact on national security, individuals, and organizations. FedRAMP High authorization involves the most rigorous security controls and assessments to ensure the utmost protection against potential threats.
4. Risk Level: Variable
Description: FedRAMP Tailored caters to unique or specialized cloud services that don’t fit neatly into the Low, Moderate, or High categories. This level allows for customization of security controls to align with the specific risk profile and use case of the cloud service. It provides flexibility while maintaining a commitment to robust security measures.
Also, check out our article, unlocking the power of tech collaboration.
Choosing the Right Authorization Level
Selecting the appropriate FedRAMP authorization level depends on several factors, including the nature of the data being processed, the potential impact of a breach, and the specific regulatory requirements that must be met. Here’s a guide to help organizations determine which authorization level is the best fit:
1. Assess Data Sensitivity
Begin by categorizing the data that the cloud service will handle. Is it public information, sensitive but unclassified data, or highly classified information? The level of sensitivity will guide you toward the appropriate authorization level. If the data is personal health information (PHI), financial records, or other sensitive data, a higher authorization level might be necessary.
2. Evaluate Potential Impact
Consider the potential impact of a security breach. What are the consequences in terms of financial loss, reputation damage, legal implications, and national security? The more severe the consequences, the higher the authorization level you should aim for. Critical systems with potentially devastating consequences require FedRAMP High authorization.
3. Review Regulatory Requirements
Different industries and government agencies are subject to various regulatory standards. Ensure that the chosen authorization level aligns with the relevant regulations. For instance, healthcare organizations handling electronic protected health information (ePHI) need to comply with the Health Insurance Portability and Accountability Act (HIPAA), which might influence the choice of authorization level.
4. Engage with Authorizing Officials
Engage with the designated authorizing officials within your organization or agency. These individuals are responsible for making the final determination regarding the appropriate authorization level. Their expertise and insight into the organization’s risk tolerance are invaluable in making an informed decision.
5. Consider Future Growth
Anticipate the scalability of the cloud service. As your organization grows or as the scope of the service expands, the potential risks and impact might change. Select an authorization level that accommodates future growth without compromising security. Also, check out our article, social engineering: a deep dive into online scams.
The Process of Obtaining FedRAMP Authorization
Achieving FedRAMP authorization is a comprehensive process that involves collaboration between the cloud service provider (CSP), the federal agency, and a third-party assessment organization (3PAO). The process generally follows these steps:
- Initiation: The CSP expresses interest in obtaining FedRAMP authorization and initiates the process with the relevant federal agency.
- Security Assessment: The CSP engages a 3PAO to conduct a security assessment. This involves evaluating the cloud service against the specified security controls of the chosen authorization level.
- Documentation: The CSP compiles documentation that outlines how the cloud service meets the security controls. This documentation is then submitted to the federal agency.
- Agency Review: The federal agency reviews the documentation and conducts its own assessment to ensure alignment with FedRAMP requirements.
- Authorizing Official Review: The authorizing official within the agency evaluates the assessment results and grants or denies authorization.
- Continuous Monitoring: Once authorized, the CSP is required to implement continuous monitoring practices to ensure ongoing compliance with FedRAMP security requirements.
Benefits of FedRAMP Authorization
Obtaining FedRAMP authorization offers several benefits to both cloud service providers and federal agencies:
- Streamlined Security: FedRAMP provides a standardized framework for implementing security controls. This streamlines the process of assessing and authorizing cloud services, reducing duplication of efforts.
- Enhanced Trust: FedRAMP authorization signals a commitment to robust security practices. Federal agencies can trust that authorized cloud services meet stringent security requirements.
- Cost Savings: Shared security assessments and documentation reduce costs for both CSPs and federal agencies. CSPs can market their authorized status to multiple agencies, saving them time and resources.
- Market Advantage: CSPs that obtain FedRAMP authorization gain a competitive edge in the government sector, as many agencies prioritize authorized services to ensure data security.
Conclusion
FedRAMP authorization levels provide a structured approach to evaluating and managing the security of cloud services and products used by federal agencies. By considering factors such as data sensitivity, potential impact of breaches, regulatory requirements, and future scalability, organizations can determine the most suitable authorization level. Achieving FedRAMP authorization demonstrates a commitment to data security and opens doors to opportunities in the government sector. As technology continues to advance, FedRAMP plays a pivotal role in safeguarding sensitive information and maintaining the integrity of critical government operations.
About Author
My name is Manpreet and I am the Content Manager at Scrut Automation, one of the leading risk observability and compliance automation SaaS platforms. I make a living creating content regarding cybersecurity and information security. Manpreet can be reached online at manpreet@scrut.io and at our company website https://www.scrut.io/