Table of Contents
Introduction — Why Social Engineering Is Still Winning
Social engineering remains highly effective because it targets predictable human behavior rather than technical flaws; behavior-based defenses are the most reliable way to reduce real-world risk.
Social engineering works by exploiting human psychology (trust, urgency, authority), and the most reliable way to prevent it is layered protection that combines human verification habits, hardened processes, and supporting technical controls.
This guide is for beginners who want clarity and professionals who want practical depth. It is not a deep red-team manual; the focus is defense and risk reduction.
What Is Social Engineering?
Social engineering is the practice of manipulating people into revealing confidential information or performing actions that compromise security.
Unlike malware or software exploits, social engineering targets decision-making under pressure.
Plain example:
A fraudster impersonates your bank and urgently asks for your one-time password (OTP). No hacking tools are required, the victim provides access voluntarily.
Why attackers prefer it
- Lower cost than technical exploits
- Works against well-secured systems
- Scales easily with automation
- Bypasses many traditional defenses
Authoritative reports such as the Verizon Data Breach Investigations Report consistently show the human element in a large share of breaches.
Why Social Engineering Works
Most articles stop at “be careful.” That advice fails because social engineering succeeds predictably, not randomly.
| Human Bias | How Attackers Exploit It | Illustrative Scenario |
| Authority bias | Impersonate executives or banks | “CEO requests urgent wire.” |
| Urgency effect | Force rushed decisions | “Account will be locked in 10 minutes.” |
| Trust familiarity | Spoof known vendors | Fake invoice from real supplier name |
| Scarcity pressure | Limited-time bait | “Claim refund today only.” |
| Cognitive overload | Target busy employees | End-of-quarter payment rush |
Types of Social Engineering Attacks (Modern Landscape)
Below is a defensive overview of the most common attack categories.
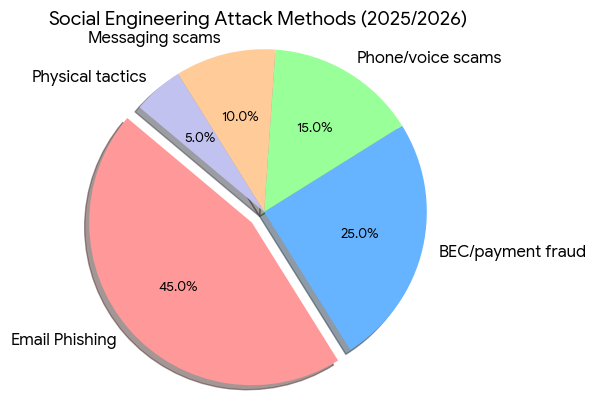
Phishing
Mass emails are designed to steal credentials or deliver malware.
- Typical targets: general users
- Failure pattern: users trust familiar brands
- Defensive focus: domain verification + MFA
Spear Phishing
Highly targeted messages using personal or company data.
- Typical targets: employees, managers
- Failure pattern: message feels context-aware
- Defensive focus: out-of-band verification
Business Email Compromise (BEC)
Executive or vendor impersonation to trigger payments.
- High-risk roles: finance teams, executives
- Common impact: large financial loss
- Referenced frequently in reports from the FBI Internet Crime Complaint Center
Pretexting
Fabricated stories are used to extract information.
Example: Fake IT support requesting password reset.
Baiting
Victims are tempted by something attractive.
Example: infected USB labeled “Salary Data.”
Tailgating (Piggybacking)
Unauthorized people follow someone into secure areas.
Quid Pro Quo
Attackers offer help in exchange for access.
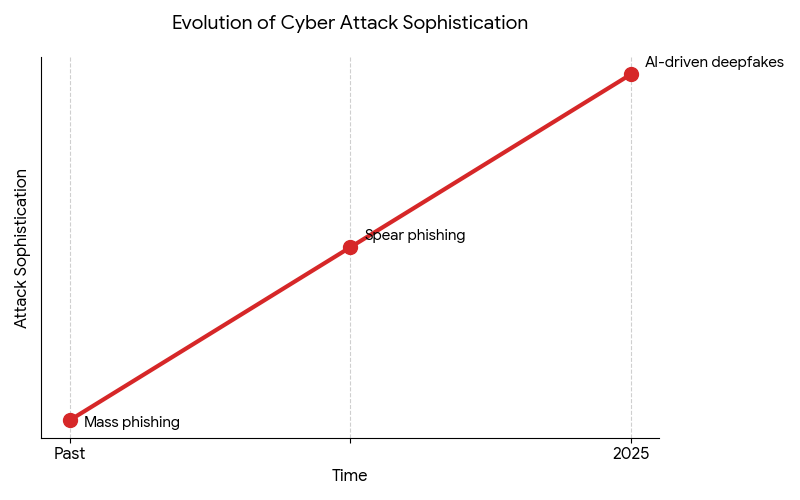
AI-Powered Voice & Deepfake Scams (Rapidly Rising)
What changed recently
- Voice cloning in minutes
- Perfect grammar phishing
- Real-time multilingual fraud
- Synthetic video impersonation
Illustrative scenario:
A finance manager receives a voice message that perfectly mimics their CFO requesting an urgent vendor payment.
Security agencies like the National Cyber Security Centre have warned about the growing realism of AI-enabled fraud.
Anatomy of a Social Engineering Attack
| Stage | Attacker Goal | Defensive Opportunity |
| Reconnaissance | Gather target info | Limit public exposure |
| Trust building | Establish legitimacy | Domain and identity checks |
| Exploitation | Trigger action | Verification pause |
| Execution | Victim complies | Approval controls |
| Exit | Remove evidence | Logging and monitoring |
Warning Signs of Social Engineering Attempts
Email red flags
- Unexpected payment requests
- Slight domain misspellings
- Emotional pressure language
- Requests to bypass normal process
Phone call red flags
- Requests for OTP/password
- Refusal to allow callback
- Authority intimidation
- “Act now” pressure
Messaging app scams
- Unknown number claiming to be a contact
- Investment or job bait
- UPI or wallet payment push
In-person manipulation signs
- Unescorted visitors
- Badge tailgating
- Fake vendor urgency
Behavior-Based Defense Framework
Most organizations overinvest in tools and underinvest in human-safe workflows.
The winning model: People + Process + Technology.
For Individuals
High-impact habits:
- Verify payment or credential requests through a second channel
- Never share OTPs or passwords
- Use password managers
- Enable multi-factor authentication
- Pause whenever urgency appears
Reality check: Awareness without habit change provides limited protection.
For Employees
Workflow controls that actually work:
- Mandatory callback for payment changes
- Dual approval for transfers
- “No-blame” reporting culture
- Clear escalation paths
- Financial process hardening
Failure pattern to watch: Employees who feel punished for slowing down.
For Organizations
Structural defenses:
- Phishing simulation programs
- Finance workflow segmentation
- Identity monitoring
- Zero-trust access models
- Executive impersonation drills
Technical Controls That Actually Help
| Control | What It Stops | Limitation |
| MFA | Credential theft | Can be socially engineered |
| Email filtering | Mass phishing | Less effective vs spear phishing |
| Domain monitoring | Spoof detection | Reactive control |
| Identity analytics | Account takeover | Needs tuning |
Trend Graph — Rising Sophistication of Social Engineering
Pie Chart — Where Social Engineering Typically Hits
Conclusion
Social engineering works because it targets human behavior, not just technology. As attacks become more convincing—especially with AI—the most effective defense is a layered approach that combines verification habits, strong processes, and supportive security tools. Individuals and organizations that design for human risk, not just technical threats, will be far better protected in 2025 and beyond.
Frequently Asked Questions
Is social engineering illegal?Yes. It typically involves fraud, impersonation, or unauthorized access and is prosecutable in the USA, UK, and India.
What is the difference between phishing and social engineering?Phishing is one technique within the broader category of social engineering.
Can antivirus stop social engineering?No. Antivirus may block malware but cannot prevent human manipulation.
Who is most at risk?Finance staff, executives, customer support teams, and highly connected individuals.
How do companies train employees effectively?Through simulation-based training, workflow controls, and reinforced verification culture—not awareness slides alone.