If you are in the market for a new smart lock, you might be wondering which features and capabilities you should go for. These factors are influenced mainly by technology trends in the broader market, and you will need to consider how the product you are going for might hold up in the near future.
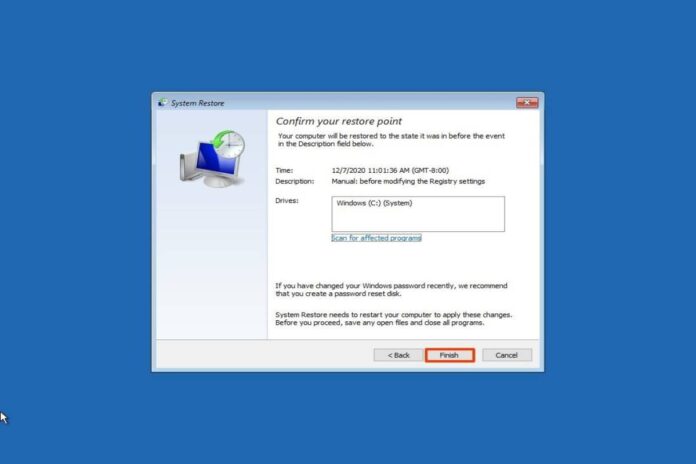
Thankfully, a WELOCK smart door lock is a long-term investment. Manufacturers often go the extra step of equipping them with over the air (OTA) update capabilities that can fix bugs and improve the user experience.
Six Key Trends In The Smart Door Lock Industry That You Should Consider When Shopping For A Smart Door Lock
Biometrics
Technological breakthroughs in miniaturized biometric sensors have enhanced smart lock authentication capabilities. These use personally identifiable biomarker data such as face recognition, palm recognition, fingerprint recognition, And iris recognition. Voice recognition is also supported on most smart door locks with audio capabilities. When purchasing a smart door lock, you should look for one that offers multiple biometric authentication options to suit each specific use.
On top of biometrics, you should also consider getting a smart door lock with other keyless entry options such as keypad locks and smart card doors.
Video and audio
Over the past couple of years, video and audio recording capabilities have improved partly due to the growth of the smartphone industry. The current market trends indicate more comprehensive adoption of video and audio-capable smart door locks, especially as homeowners look to remotely interact with whoever is at the door before unlocking it. Smart door locks should be capable of two-way audio.
Remember that quality matters wherever you are dealing with security footage from the smart door lock. Opt for smart door locks with HD resolution cameras or more, as you will get clearer images and even digital zoom.
Encryption
Smart lock manufacturers are starting to realize the need for strong data protection and privacy guarantee. Look for smart door locks that adhere to current compliance standards when it comes to data encryption. These rely on military-grade PI encryption protocols to secure all information exchange between the smart door lock and your smart devices.
Data encryption is a smart lock that doesn’t just apply to wireless connection but also on the device level, whereby all recorded video and audio data gets encrypted.
Power source
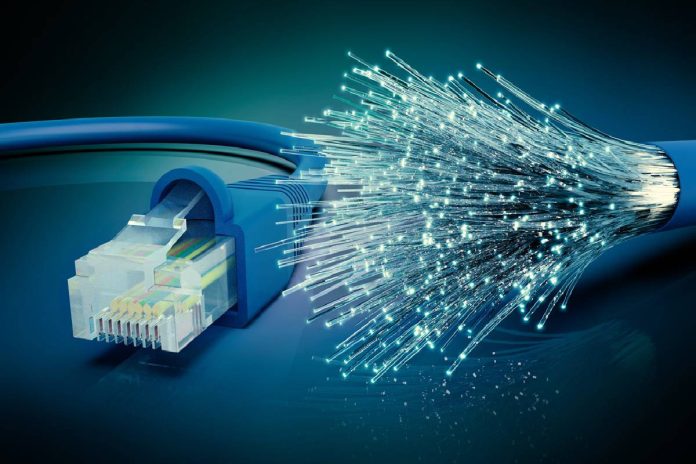
Smart door locks require a power source to operate, with most designs relying on rechargeable AA batteries, with some models using rechargeable lithium batteries. Market trends in this segment have led to the rise of power over ethernet (PoE) powered smart door locks that use the same connection for data transmission, thus eliminating wireless overcrowding.
Depending on how close your door is to a power source, you will need to consider if it is possible to get a wired connection to the smart door lock. You can also consider getting a smart door lock that is compatible with power bank charging and remote low battery notifications.
Connectivity
If the current market trends are anything to go by, consumers are now opting for smart door locks with multiple wireless connectivity options. These use various wireless protocols that can even link up to internet of things (IoT) capable homes.
Upgradeability
Just like your phone, the smart door lock will receive over-the-air software updates to fix bugs and improve the user experience. Manufacturers have adopted firmware updates to fix critical functions and fix known vulnerabilities keeping your household safe. In some cases, you may need to replace the whole smart lock if the chip used can no longer support additional updates or when you need new capabilities such as facial recognition.
Should you go for the most feature-packed smart door lock?
While it might sound enticing to go for the latest and greatest when shopping for a door lock in the hopes of it being a long-term investment. It’s always more nuanced than that. You have to consider if the manufacturer tends to support the device via OTA and the hardware capabilities you are getting out of the box. Avoid falling for marketing gimmicks and instead opt for futures with positive reviews from actual buyers.